Heat traces are left on the laptop or computer as you type your password on the keyboard. These heat traces can be picked up by hackers using a thermal imaging camera which they can use to scan your keyboard that you used to type the password. A team of researchers at the University of California, Irvine UCI found that key presses can be detected within half a minute after the first key was pressed using the solutions offered by FLIR cameras. These cameras have infrared and heat detecting ability.
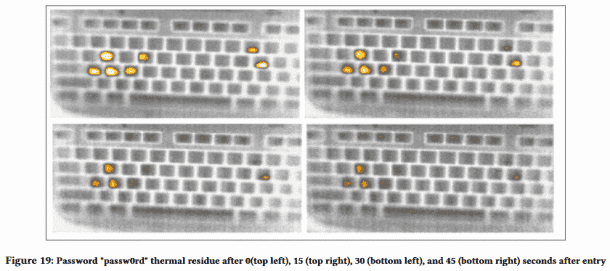
After a minute has passed, the thermal scans can be used to obtain partial passwords. The team found that the thermal residue evaporates over time and there is a time limit by which thermal energy readings can be harvested from computer or laptop. Users who are not experts were asked to guess the passwords after 19.5 and 31 seconds of entering them. Weak passwords like football took nearly half a minute for the non-experts to guess them.
The researchers concluded that using the forefingers to type, a user can leave a bigger fingerprint on each key which can lead to more heat traces left behind. As a result, more thermal noise is generated. This makes it difficult to analyze the heat traces using the FLIR camera. Those who have acrylic fingernails are less prone to thermal attacks as they type using fingernails and as a result, they leave almost no heat traces behind.
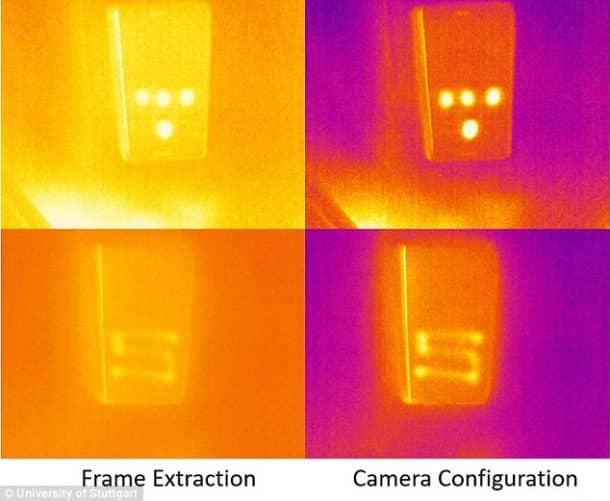
The findings suggest that the thermal imaging attacks are realistic. If you want to keep your password safe while using your computer in a public environment, you should follow the two-factor authentication. For this attack, an attacker needs to place a camera that has thermal recording feature near the computer from which it wants to steal the passwords. The research team also believes that to make sure that the passwords stay protected, there should also be an alternative way to use them. A team member stated, “As formerly niche sensing devices become less and less expensive, new side-channel attacks move from ‘Mission: Impossible’ towards reality. This is especially true considering the constantly decreasing cost and increasing availability of high-quality thermal imagers”.


