Even if you are an experienced tech savvy who does not fall prey to e-mail scams, the new Gmail phishing attack is the one you also need to avoid at all costs. According to security researchers, this scam is highly effective in tricking people.
The campaign seems to be running on sophisticated automation features. The attackers lunge at the compromised Gmail account and then, target the users on the contact list. Before launching the attack on the contact list, the criminals first go through the previously sent actual emails and attachments to the respective contacts.
Using the relevant subject line and attachments, the attackers then send an email from the hacked account to these contacts.
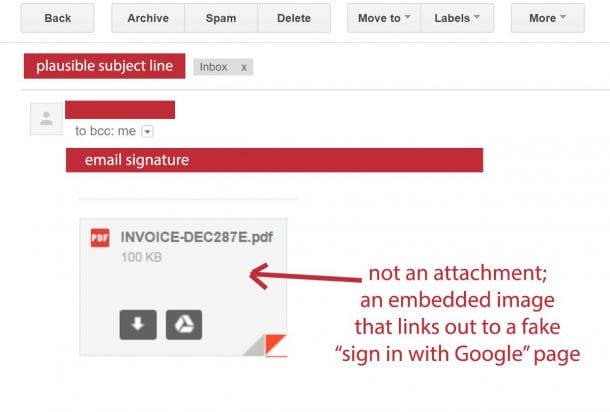
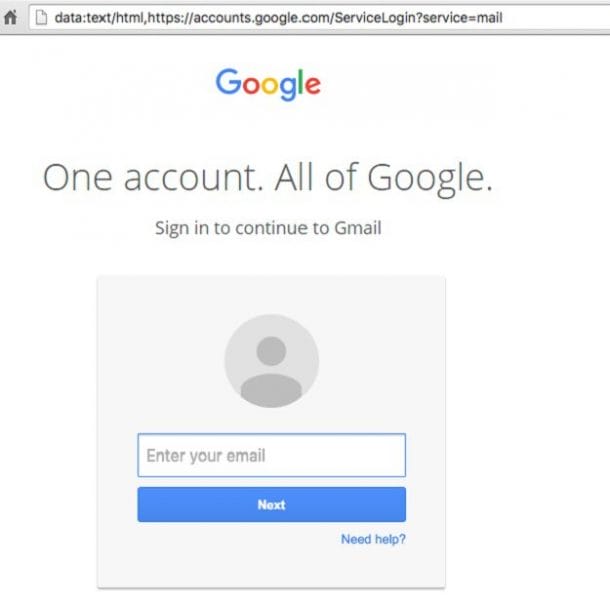
When these contacts click the attachment thumbnail, instead of opening the Gmail preview, a full web page is loaded that has a very convincing Gmail login box.
Two things that make this scam so successful are:
1) The emails are received from someone the victim knows.
2) Instead of redirecting the user to a suspicious website, a Gmail login page loads.
The browser address is padded with whitespace and https://accounts.google.com domain is enough to trick the user.
How should you protect yourself from this scam? It’s pretty simple. The first thing to do in enable two-factor authentication in Gmail. This feature will stop them from hacking into your account even after they get the password. Always, keep an eye on the lock icon next to your address bar. Beware of the websites which are not hosted on SSL-secured servers. These solutions are not foolproof because a lot of phishing sites are still hosted on secured servers.

If you think your account has already been attacked, change your Gmail password immediately. Go to the Gmail account activity page and remove all the current sessions that look suspicious.
Share this article as much as you can to create awareness about this prevalent scam!


