#Twitterhacked!! Probably trended back in February 2013 when a team of high-tech hackers managed to get partially into the user database of the popular social networking platform. What we are looking at are usernames, email addresses, user information and even encrypted passwords hacked as a result of this effort from the unknown snoopers. The attack happened right when Wall Street and New York Times had reported several intrusions in their own systems. The media was quick to point out the possible involvement of the Chinese government behind the attacks as it is common knowledge that most of these criminals with PCs originate from the world’s most populous country. In the case of Twitter, the attack only lasted for a few moments as it was quickly discovered and dealt with, but not before, a lot of user data was compromised even though in bits and pieces.
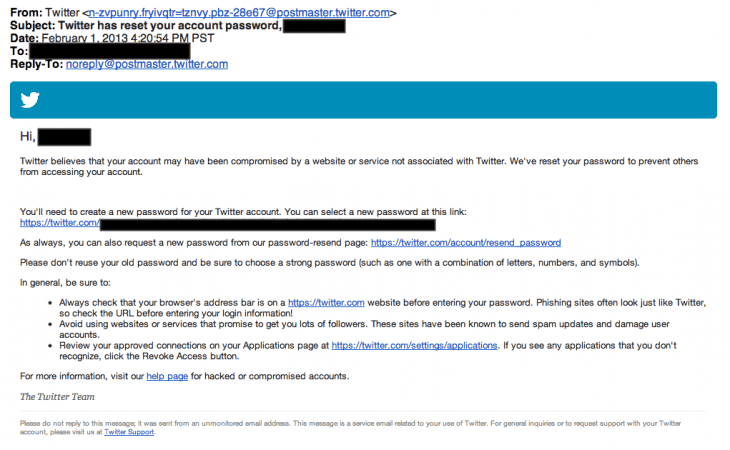
Twitter was quick to follow suit and asked the users who had been attacked to get their password changed and not use the obvious kinds on their logins anymore. It was probably the same time around which the multi-platform identification was started by social networking websites to establish the authenticity and security of the users’ accounts. Bob Lord, the head of Twitter’s Information Security department said
“This attack was not the work of amateurs, and we do not believe it was an isolated incident. The attackers were extremely sophisticated, and we believe other companies and organizations have also been recently similarly attacked. For that reason, we felt that it was important to publicize this attack while we still gather information, and we are helping government and federal law enforcement in their effort to find and prosecute these attackers to make the Internet safer for all users.”
So, Twitter didn’t hold back the hacking attempt and tried to warn the users as quickly as possible. Also, Twitter took the step of advising users of disabling Java in their systems. The same was always advised by the Department of Homeland Security as well. Oracle, Java’s parent company, was also notified of the various problems associated with the Java Runtime Environment and its potential use in hacking.
So, be careful what you upload on social media and just don’t tell it everything just because everybody else is doing it. We might not see the kind of hacking done on social media platforms, but hackers and stalkers might not even need that. Just see your profile and see the stuff available publicly for you!


