We have been covering articles about cars and how engineers are busy in coming up with performance based cars. While their research continues and new breakthroughs are being achieved, there’s another group which is working to exploit weaknesses in cars and how they work.
 What we have for you today is a $20 gadget which is capable of hacking any car and giving the hacker control to car’s headlights, locks, steering and brakes. The gadget is smaller when compared to a smartphone and hence portable.
What we have for you today is a $20 gadget which is capable of hacking any car and giving the hacker control to car’s headlights, locks, steering and brakes. The gadget is smaller when compared to a smartphone and hence portable.
The gadget is known as CAN Hacking Tool (CHT) and is capable of being fitted to any car’s Controller Area Network in just a couple of minutes and once it has been fitted, a virus like code can be run through the vehicle’s system. The invention comes from Javier Vazquez Vidal and Alberto Garcia Illera who are Spanish researchers linked with security. The gadget was shown off back in 2013 at Black Hat Conference in Las Vegas. The designers have plans for organizing a demonstration at Singapore in March for the same conference.
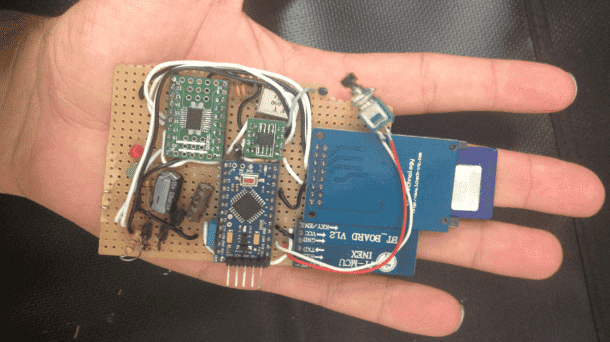 Vazquez said; ‘It can take five minutes or less to hook it up and then walk away. We could then trigger it to do whatever we have programmed it to do.’ How is it possible? Nowadays almost all the cars come with softwares which are built-in and rely on an OS that is somewhat similar to OS used in phones and computers. Hackers exploit the vulnerabilities of this operating system for their gadget to work. Speaking in terms of physical contact, the gadget’s four wires need to be attached with unique outputs which belong to vehicle’s controller network. A computer chip is employed to get away from any encryption before the actual reading or writing can take place and guess how much does the chip cost? It costs $1 only!
Vazquez said; ‘It can take five minutes or less to hook it up and then walk away. We could then trigger it to do whatever we have programmed it to do.’ How is it possible? Nowadays almost all the cars come with softwares which are built-in and rely on an OS that is somewhat similar to OS used in phones and computers. Hackers exploit the vulnerabilities of this operating system for their gadget to work. Speaking in terms of physical contact, the gadget’s four wires need to be attached with unique outputs which belong to vehicle’s controller network. A computer chip is employed to get away from any encryption before the actual reading or writing can take place and guess how much does the chip cost? It costs $1 only!
Among many other commands which will be at the disposal of the hacker, the hacker is able to disable the brakes, engaging the airbag, locking up the car and enabling/disabling the alarm system. This gadget is not the first of its kind and according to Valasek; ‘Academics have shown you can get remote code execution. We showed you can do a lot of crazy things once you’re inside.’
 In simple words, the opportunities are limitless and once we tap into the source, we have a myriad of options. However, is this technology and research going to prove useful or just a nuisance still remains to be seen.
In simple words, the opportunities are limitless and once we tap into the source, we have a myriad of options. However, is this technology and research going to prove useful or just a nuisance still remains to be seen.



Fast Six technology coming soon to reality. T_T