Due to a small typing error, millions of emails intended for the US military have mistakenly been sent to Mali, a country allied with Russia. This error has occurred because the US military’s email domain, “.mil,” has been confused with Mali’s domain, which ends in “.ml.” Some of these emails contained sensitive information, such as passwords, medical records, and the travel plans of high-ranking officers.
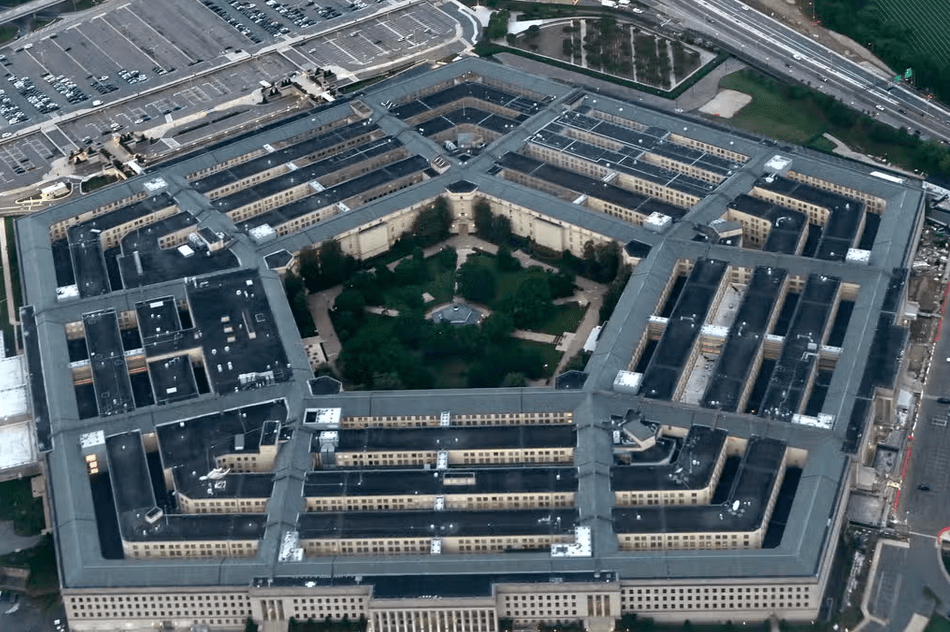
The Pentagon, aware of the issue, has taken measures to address the situation. This problem was actually identified over a decade ago by Johannes Zuurbier, a Dutch internet entrepreneur. Since 2013, Zuurbier has been responsible for managing Mali’s country domain and has reportedly collected tens of thousands of misdirected emails in recent months.
Although none of these emails were labeled as classified, they did contain various types of information, including medical data, maps of US military facilities, financial records, official trip plans, and diplomatic messages.

Concerned about the potential risks, Mr. Zuurbier wrote a letter to US officials this month, emphasizing that his contract with the Mali government was soon coming to an end, which could lead to adversaries of the US exploiting the situation. Mali’s military government was scheduled to assume control of the domain on Monday.
While emails marked as “classified” and “top secret” are transmitted through separate secure systems, current and former US officials assert that even seemingly innocuous information can be valuable to adversaries, especially if it contains personal details about military personnel.
The risk of “typo-squatting,” a type of cyber-crime that exploits misspelled domain names, is common, and adversaries hope that individuals will make mistakes that can be exploited for nefarious purposes.
“Those sorts of communications would mean that a foreign actor can start building dossiers on our own military personnel, for espionage purposes, or could try to get them to disclose information in exchange for financial benefit,” Steven Stransky, a lawyer who previously served as senior counsel to the Department of Homeland Security’s Intelligence Law Division said. “It’s certainly information that a foreign government can use.”
He also said that even seemingly harmless information could prove useful to US adversaries, particularly if that information included details of individual personnel.
The US military is fortunate that this issue was brought to their attention and that the misdirected emails were going to Mali’s government domain rather than falling into the hands of cyber criminals, according to Lee McKnight, a professor of information studies at Syracuse University.
The Department of Defense spokesperson confirmed that they are aware of the problem and are taking it seriously. Measures have been implemented to prevent “.mil” emails from being sent to incorrect domains, including blocking them before they are sent and notifying senders to validate the intended recipients.
Both McKnight and Steven Stransky, a lawyer who previously worked for the Department of Homeland Security, emphasized that human errors are major concerns for IT specialists in both government and the private sector.
“Human error is by far the most significant security concern on a day-to-day basis,” Mr Stransky said. “We just can’t control every single human, every single time”.


