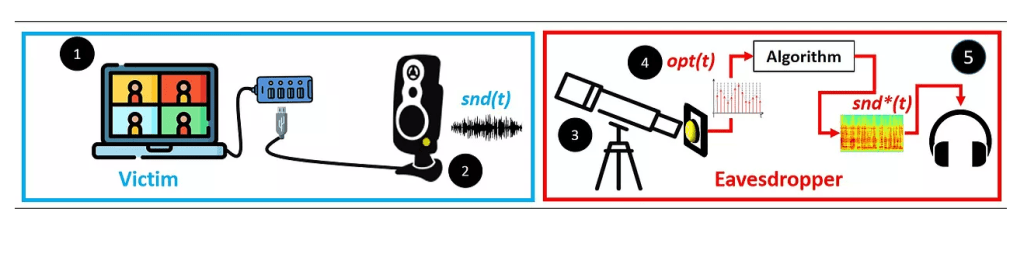
A new attack method called the “Glowworm Attack” has been pitched by researchers of the Ben-Gurion University of Negev. It operates with optical emanations from a device’s power indicator LED to produce sound from connected surroundings. The catch is that it is more than capable of spying on electronic conversations.
“We present the Glowworm attack, an optical TEMPEST attack that eavesdroppers can use to recover sound by analyzing optical measurements obtained via an electro-optical sensor directed at the power indicator LED of various devices (e.g., speakers, USB hub splitters, and microcontrollers),” write the researchers in their abstract.
“We analyze the response of the power indicator LED of various devices to sound and show that there is an optical correlation between the sound that is played by connected speakers and the intensity of their power indicator LED due to the facts that: (1) the power indicator LED of various devices is connected directly to the power line, (2) the intensity of a device’s power indicator LED is correlative to the power consumption, and (3) many devices lack a dedicated means of countering this phenomenon.”

A lot of experimental situations were put forth to test the Glowworm Attack. The attacker has been proven to be able to eavesdrop on the victim in various different situations. The Glowworm Attack can conveniently provide good intelligibility from a 50 ft (15 meters) distance and with fair intelligibility from 115 ft (35 meters).

Devices such as Google Home Mini, Google Nest Audio, Logitech – Z120 Speakers, S120 speakers, Sony – SRS-XB33, SRS-XB43, and Raspberry Pi – 3, 4. are vulnerable to the Glowworm Attack. But the manufacturers of these will definitely keep in view the possibility of this attack while designing and planning the features in their devices.


